What is Fileless Malware?
- Apr 24
- 6 min read

Most people picture malware as a bad file, something you accidentally download, something your antivirus flags and removes. Fileless malware doesn't work that way.
It never touches your hard drive. It runs entirely in memory, hidden inside tools your operating system already trusts. There's no suspicious file for a scanner to find, because there is no file.
According to CrowdStrike's 2026 Global Threat Report, 82% of attacks detected in 2025 were 'malware-free', meaning attackers avoided dropping traditional malicious files entirely, instead relying on credentials, built-in system tools, and techniques like fileless execution that traditional antivirus was never designed to catch.
These types of attacks are difficult to eliminate because they reside within the system and have not been downloaded like other malware. This also makes it harder to detect through traditional malware protection and antivirus software. That's not a design flaw attackers stumbled onto. During fileless attacks, infiltrators are able to take control and deploy malicious threat actors by exploiting vulnerable systems that a user may use daily, such as Microsoft Word or the Chrome browse.
It can often go under the radar for much longer than typical malware attacks that infect files. However, this does not mean that it is impossible to detect and clear these types of attacks. While it may be harder to find, there are a few ways to detect this type of attack.
How Does Fileless Malware Work?
The defining characteristic of fileless malware is this: it never writes anything to your hard drive. It can access legitimate system processes that administrators can usually trust and hide within. It also does not leave the usual file-based traces that are easier to detect. Fileless malware does not create any new files or programs for antivirus programs to detect. Traditional malware drops a file, an executable, a document with embedded code, or a script. Security tools are designed to look for those files. Fileless malware skips that step entirely. Instead, it loads directly into memory and uses tools your operating system already provides, PowerShell, Windows Management Instrumentation (WMI), and other built-in administrative utilities that IT teams use legitimately every day. A user may click a link or open a document that contains fileless malware, which includes a script that can directly infect a device's memory. So, attacks can still happen in the traditional way, but how they behave once they are on your device is very different.
Think of it this way: instead of breaking in with a crowbar, the attacker borrows your own keys.
Because those tools are supposed to be running, nothing raises an alarm. Because there's no malicious file on disk, a file scanner has nothing to find.
Since no new files attack the hard drive, standard file-scanning tools may miss these threats completely. The attack blends in with normal system activity on the surface.
Types Of Fileless Malware Attacks
As briefly mentioned, there are two main types of fileless malware attacks, including:
Memory Code Injection
Attackers inject malicious code directly into a legitimate process already running in memory, a browser, a business application, or a PDF reader. From the outside, the process looks completely normal. Underneath, it's executing the attacker's instructions.
Windows registry manipulation
The Windows registry is the database that controls how your system behaves at a fundamental level. Windows registry manipulation occurs when hackers use a malicious link or file to exploit the trusted Windows system. They hide within the most trusted parts of the system and may not trigger any alerts until they begin to act. Because the registry is a core part of the operating system, this activity often looks indistinguishable from a legitimate system configuration.
PowerShell-Based Attacks
PowerShell is one of the most powerful administrative tools built into Windows, and one of the most exploited. Attackers use it to run malicious commands entirely in memory, leaving no trace in files. Attackers use legitimate tools like PowerShell to execute malicious scripts directly in memory. Because PowerShell is widely used by IT teams, these attacks often blend in with normal system activity and evade detection.
Living Off the Land (LotL) Attacks
Living off the land is the broader strategy underlying most fileless attacks: use what's already installed. No outside tools. No unusual software. These attacks rely on built-in system tools (such as command-line utilities and administrative tools) rather than on external malware files. By using trusted programs already installed on the system, attackers can carry out malicious actions without raising suspicion.
Stages of a Fileless Attack
These types of attacks take time to occur. There are four main stages of a fileless attack.
Initial Access
This stage involves a hacker gaining initial access into a system or network. Every fileless attack starts with a conventional entry point. A phishing email with a malicious link. A document with embedded macros. A compromised website that executes code in the browser. Credentials that were already stolen in a previous breach. Any of these methods are enough to grant a hacker access and begin a fileless attack.
Steal Important Credentials
Once inside, the attacker's first priority is elevating access. Tools like Mimikatz can extract stored credentials directly from system memory: usernames, passwords, authentication tokens. Tools like this allow hackers to go seamlessly through systems without triggering any alerts. With valid credentials in hand, the attacker can move through your environment as if they belong there, because as far as the system is concerned, they do.
Persistence
Fileless malware has one structural weakness: a reboot can wipe it from memory. Attackers account for this early. Before the system is ever restarted, they embed themselves into scheduled tasks, startup scripts, or registry entriesThis way, hackers do not have to repeat the initial stages of the fileless attack. Hackers can create scheduled tasks and registry modifications to prevent loss of access, even after reboots.
Extract Data
With persistent access and elevated credentials, the attacker locates what they came for: customer records, financial data, intellectual property, credentials for other systems, and begins exfiltrating them. This can happen over a long period of time as these attacks go undetected. Hackers can remain in the system for as long as they need to gather data and often leave without notifying anyone.
How To Detect Fileless Malware Attacks
While these attacks are harder to detect, there are ways to do so. the antivirus software most people are familiar with, like Norton, McAfee, the box you pick up at Best Buy or Walmart, was built to catch file-based threats. It looks for malicious files, matches them against a database of known signatures, and flags what it finds. That model works reasonably well against traditional malware. Fileless malware doesn't create files. Which means those tools are looking for something that isn't there. Detecting fileless attacks requires a fundamentally different approach.
Upgrade to endpoint detection and response (EDR). Consumer antivirus tools have added basic behavioral monitoring, but they aren't designed for fileless malware, which executes in memory, hijacks processes, and operates below the file system. Enterprise-grade EDR platforms like SentinelOne and CrowdStrike are built for this, monitoring process behavior, inspecting memory in real time, and detecting anomalies that file-based tools miss. For businesses handling sensitive data or with many devices, adopting such platforms is the essential baseline.
Monitor for lateral movement. Attackers move within networks, escalating access. Monitoring for unusual account activity, such as odd logins, unexpected system access, or abnormal patterns, can help detect attacks early. This method typically consists of three stages: reconnaissance, escalation, and network traversal.
Use Indicators of Attack (IOA) Detection: This method works by identifying the activity associated with the malware, rather than a specific file added to your system.
Invest in continuous threat hunting rather than reactive security that waits for alerts. Threat hunting is proactive: actively searching for signs of compromise using EDR tools that provide visibility. Small and mid-sized businesses should work with a managed security partner to deploy and monitor security tools, as tools alone don't provide protection; they need to be managed.
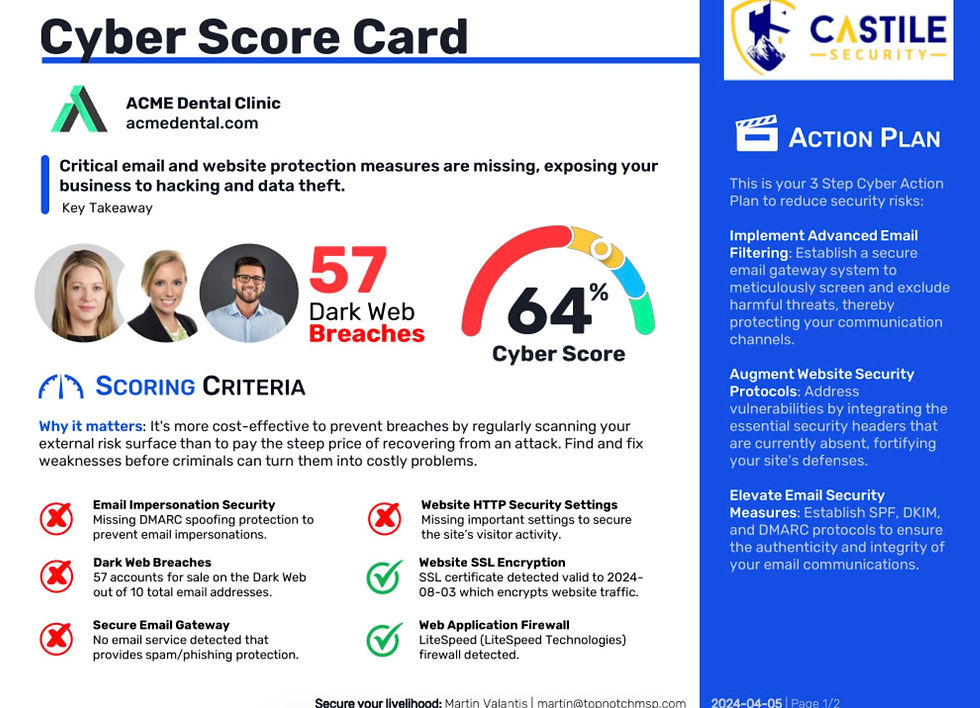
How Castile Security Can Protect Against Fileless Malware
Defending against fileless malware requires visibility into behavior, not just files, which means the tools and practices most businesses have in place by default aren't enough.
At Castile Security, we start with a 3D DeepDive to identify your current gaps. From there, the work typically involves deploying endpoint detection and response (EDR) tooling that monitors behavior in real time, tightening access controls so that even if an attacker gains initial entry they can't move freely, and training your team to recognize the delivery mechanisms, phishing emails, suspicious links, unexpected document prompts, that most fileless attacks depend on to get started.
If you want to know where you actually stand, an assessment is the right first step.
FAQ
What are the symptoms of fileless malware?
Fileless malware is designed to blend in, which makes symptoms easy to attribute to something else. Common symptoms include: unusual slowdowns, unexpected PowerShell/command activity, odd authentication prompts, unexplained admin changes, suspicious scheduled tasks/registry changes, unusual network traffic, and accounts logging in at strange times or from unfamiliar locations.
Is fileless malware a virus?
Not in the traditional sense. "Virus" has become shorthand for anything malicious, but technically it refers to code that copies itself by attaching to files. Fileless malware doesn't create files, doesn't land on disk, and often doesn't replicate that way. It is a malicious activity that is executed through legitimate system tools, usually without leaving the typical file traces that antivirus detectors expect.
How is fileless malware delivered?
The initial delivery often looks like a conventional attack: a phishing email, a malicious link, a document with embedded macros, a compromised website, or credentials obtained through a previous breach. What makes fileless malware distinct isn't how it arrives; it's what happens next. Once triggered, it executes in memory rather than writing to disk, which is exactly where most security tools stop looking.




Comments